What is Mobile Apps Security? Best Practices 2026

In the context of the constantly evolving digital mobility, mobile app security is one of the primary and at the same time multifaceted concepts referring to measures and tools needed to enhance the protection of mobile apps used on portable devices. Primarily, mobile application security is the careful integration of processes that aim at countering a range of threats, from advanced malware penetration to data leakage through insecure networks. This discipline requires mastery of app scanning techniques, and complex, highly developed automated systems designed to examine mobile application codes and configurations and pick out potential weaknesses that could threaten users’ privacy.
Thus, it becomes clear that the security of mobile applications requires the implementation of enhanced encryption techniques and strict authentication mechanisms with constant monitoring and preparation against any threats concerning the safety of users’ data as well as compliance with modern regulations.
I. What is Mobile Apps Security
Mobile apps security can be defined as the defense mechanism or strategy that has been put in place to ensure the protection of mobile applications from various security risks and threats. Living in a world where the use of mobile devices is almost essential in people’s everyday lives, the question of the need for secure mobile apps is beyond debate. This involves a holistic approach covering not only the software layer but also the hardware layer of the mobile devices and the information contained to prevent access of the information by unauthorized persons, leakage of information, and other cyber perils.
In its simplest understanding, mobile apps security is establishing strong security principles and processes to establish an effective security mobile app system. This incorporates the use of secure code, encryption both in transit and in storage, strong authentication, and authorization measures, and repeating security audits. It is to prevent possible security threats and guarantee that security threats are only a short amount of time and that they are eliminated.
Additionally, there are considerations of secure mobile apps against different kinds of threats like malware, phishing, and unauthorized access to data. This requires the constant assessment and modification of these measures to address new threats that may emerge and changes in the various cyber-attacks. Software solution providers are obliged to be wary and mindful of possible security risks and take desirable measures to make their solutions unassailable.
In conclusion, mobile application security is a complex area that refers to protecting the applications through careful preparation, monitoring, and implementing actions against threats. Major app security, therefore, can go a long way in helping app users feel safer and secure when using the applications in question, and this, in turn, will promote the overall trust level in such applications among their users.
II. Mobile Apps Hacking Statistics
Consumers frequently rely on organizations to evaluate their mobile app security measures before making them accessible. However, IBM’s research uncovered startling realities.
- 50% of enterprises have no budget for securing their mobile applications.
- 40% of businesses do not examine the code of their mobile applications for security flaws.
- In 2014, cyberattacks compromised 1 billion personal data records, and at any given time, mobile malware affects 11.6 million mobile devices.
- On average, less than half of the mobile apps developed by a company are tested, and 33% are never tested for mobile app security.
The aforementioned figures provide sufficient motivation for hackers to exploit flaws in mobile app security, and they attempt to exploit any or all unsecured codes.
III. Why Mobile Apps Security Important
It is therefore important to ensure that mobile apps are secured taking into consideration the use of mobile apps today in personal, business, and financial aspects.
Protection of Sensitive Information
Freemium apps usually process a significant amount of personal information that can be considered as personal identification data, money transactions, or secure messages. This data is exposed to insecure threats such as unauthorized access, data, and cyber-attacks resulting in financial loss and identity theft if the security of the mobile app is not well developed. The importance of having a detailed security plan for mobile applications reduces the risk of adverse effects and safeguards individuals who can suffer from it.
Defense Against Sophisticated Cyber Threats
It is, therefore, a common notion that cybercriminals always seek out new techniques to target the security weaknesses of mobile applications. Mobile apps security entails preventative measures that can be used to detect such incidences and prevent such vulnerabilities from being exploited in the app. This proactive approach is necessary to monitor and prevent new malicious attacks and to maintain the application’s security against new threats on the Internet.
Enhancement of User Trust and Confidence
Since the security and privacy aspects that customers are very sensitive to, they are more likely to use and appreciate applications that address this particular issue. Adhering to security mobile apps keeps the users engaged and possesses a good image, which is paramount to apps’ success and sustainability. The implication is that any security threats pose a major risk to an application’s reputation, users’ trust, and subsequent usage; besides the dangerous prospects of financial losses. As such, organizations must emphasize the security of mobile applications to sustain and increase users’ trust.
Regulatory Compliance and Legal Requirements
Some sectors like the financial sector or the healthcare sector have their policies and legal requirements regarding data protection demanding optimum security measures. Noncompliance with the above-regulated policies leads to severe ramifications and legal implications, making it crucial to have robust security features for mobile applications. It is important to keep security mobile apps in check for such requirements to enhance legal compliance and safe user data.
Safeguarding User Experience and Application Integrity
Ensuring mobile apps security is critical since this makes the layout protective and secure for users. This also contributes to the improved user experience of the application as well as protecting the application from vulnerabilities and future failures, thereby continuing its success and stability. A secure application means an application that does not pose any risk to the end user and their data and also helps maintain the reputation and functionality of the application.
IV. How Does Security Mobile Apps Work
Mobile apps security is a process that involves the use of advanced technologies, vigorous processes, and implementable tactics that prevent mobile applications from being vulnerable to security issues. The primary aim is to keep the data safe, stop people who shouldn’t see it from getting access, and ensure the mobile app is private, always accessible, and works well with other systems. This involves a complex process of making a secure mobile app environment, and it includes several key parts.
Secure Coding Practices
Ensuring new code is written securely is the backbone of mobile application security. Programmers themselves need to follow certain guidelines and rules to ensure their code is immune to basic attacks like buffer overflows, SQL injection, or cross-site scripts, among others. Developing security into the software development lifecycle means that possible security vulnerabilities have to be spotted at an early stage thus preventing exploitation.
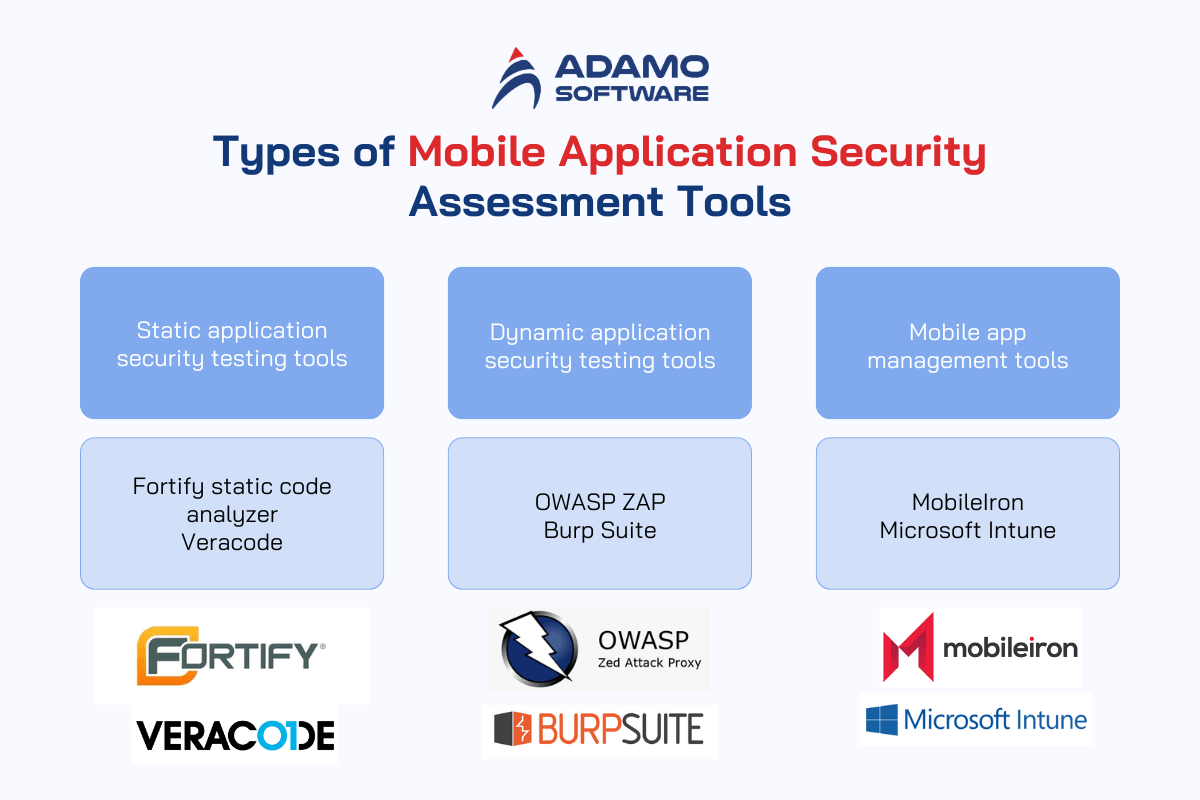
Mobile App Scanning Tools
Mobile app scanning tools play an important role in detecting such threats and mitigating related risks. These tools crawl through the code, configuration, and network usage of the application to identify possible security bugs. They give an overview of the specific weaknesses that were found which assists the developers fix such problems before the application is deployed. Regular practice of the mobile app scanning tools assures that fresh threats are detected and dealt with in real time.
Encryption and Data Protection
Among the most important things concerning mobile apps security is encryption. Such a way of coding helps to protect information not only while it is being sent but also while it is stored. Coding methods guarantee that all information sent through the app or saved in its storage is private and protected from exposure to unwanted eyes. This will help prevent unauthorized access and ensure more security for the data of the user, even if an attacker captures the device.
Authentication and Authorization Mechanisms
Security monitoring is another crucial requirement to help organizations track and respond to security issues in real time. This is done through the application of analytical and monitoring techniques which enable the detection of anomalous behavior and dangers. An incident response solution assists in fast and appropriate reactions to security incidents to reduce costs from compromised applications and their users.
Security Monitoring and Incident Response
Security audits and vulnerability scanning should be conducted in the mobile app ecosystem periodically. These practices involve conducting a mock attack on the application to determine the weaknesses present and the efficiency of the existing security solutions. This way the developers are always on the lookout for new threats that are likely to come up and keep on updating the application to make it secure all the time.
Regular Security Assessments and Penetration Testing
Regular security assessments, penetration testing included, are essential in keeping a mobile app environment secure. These are exercises whereby the application is attacked to reveal hidden vulnerabilities and test efficiency for security measures put in place. A periodic assessment will keep every developer ahead of increasing application threats.
To sum up, mobile apps security comprises of secure coding styles, mobile app scan tools, encryption, suitable authentication schemes, constant monitoring, and security audits. Through these measures, developers can design mobile applications that protect the information from threats, thus safeguarding users’ data and building confidence.
V. What are the Most Common Threats in Mobile Apps
It is far too simple to compromise mobile app security. Companies desire rapid app releases, but development teams are frequently understaffed and overcommitted. Security is neglected, although it should not be. You must pay close attention to the following 9 mobile app security risks if you wish to safeguard your company’s reputation and revenue.
1. Low API Protection
If you are developing an application, you will almost undoubtedly use at least one API. A mobile app API enables one application to retrieve data from another. For instance, it is what enables a travel booking website to compile information from various hotels and airlines in an organized manner. It is also what enables Google Maps to display directions to a given location.
Most modern applications rely heavily on APIs for their functionality. Numerous developers fail to secure their APIs. They believe that bad actors will not find them engaging, but the converse is true. APIs provide access to stable, structured data, which is precisely what malicious actors desire. They will reverse-engineer your API to determine which endpoints your application utilizes, execute your application with an emulator, or utilize a mobile farm to locate access points.
How to prevent low API protection
As with many of the other hazards on this list, malicious bots pose the greatest risk of exploitation. Generally speaking, bots have no reason to use your API, so its usage is not a positive sign. A bot protection solution designed particularly for mobile app security will be able to detect and block malicious bots while allowing legitimate ones to pass.
2. Insufficient server-side controls
Modern mobile apps consist of both a client and server side. The client-side is visible to the user. This is the user interface, complete with animation and functionality. The client side relies on the server side, which is responsible for ensuring that everything functions correctly, for everything to work. Client and server typically interact via an API.
Common server-side vulnerabilities are readily exploitable via the frequently insecure API. They can include faults in code logic, weak authentication rules, insecure server configurations, and access control vulnerabilities, among others. They generally fall into 2 categories: code vulnerabilities and configuration vulnerabilities.
How to prevent insufficient server-side controls
Although the client side of an app communicates with its server side via an API, you can block numerous threats by preventing automated routines from accessing your API. While this won’t prevent manual attacks or fix server-side vulnerabilities, it will at least prevent your mobile app security from being exploited very readily.
3. Injected on the client side
Unusual data that leads to unauthorized access is one method an adversary can use to attempt to compromise your application. This data is typically transformed so that your application can interpret it as executable code. An assailant could, for instance, target a mobile SQL database by inserting a creative query that retrieves private data from other users.
SQL intrusions are only one client-side injection type. Local File Inclusion is another form, in which an attacker uploads an executable file that your app reads and executes, which can cause your app to malfunction or expose sensitive data.
How to prevent client-side injections
One of the most effective ways to prevent client-side injections is by performing appropriate input validations, i.e., checking all incoming data (including that from partners, regulators, and suppliers) to ensure that it falls within the expected parameters. Effective input validation can entail:
_ Putting into effect a minimum and maximum value range verification for data and string length.
_ Introducing a regex check that avoids “any character” wildcards such as “.” and “*”.
_ Requesting an exact match if the input data options are static.
_ Accepting only input data from a list of permitted values.
4. Insecure Storage of Sensitive Data
Frequently, mobile apps, including financial apps, store sensitive data locally. This means that your PIN, credit card numbers, passwords, login information, and other sensitive data are merely stored on your smartphone. Worse yet, they are frequently stored insecurely. If a tech-savvy individual obtains access to your device (remotely or otherwise), they can locate and steal all of your data.
Often, sensitive local data is stored insecurely due to inadequate encryption. Some mobile apps do not encrypt local data at all, which is the gravest violation. Other mobile applications encrypt local data but do not properly store the encryption keys, or they employ insecure custom encryption protocols.
How to prevent unsafe sensitive data storage
Data at rest must be adequately encrypted using a robust encryption protocol that has been widely regarded as secure by the mobile app security community for a long time. Do not attempt to perform complex actions with a custom protocol. It is much more likely that you will make a mistake and inadvertently expose sensitive local data instead of safeguarding it.
5. Hardcoded keys or a password
This is the most elementary error, but it still occurs. To make an app simpler to implement, maintain, and investigate, developers frequently hardcore passwords, API keys, or OAuth keys. This indicates that these credentials or keys are encoded explicitly within the code. When these hardcoded values are discovered because an attacker reserve-engineered your app, you leave yourself broadly open to exploitation of all kinds.
How to prevent hardcoded keys or a password
Provide developers with a password management solution that securely stores their passwords and credentials so they do not need to hardcode sensitive values. In addition, scan frequently for hardcoded passwords, and if you discover one in a live application before anyone else, promptly patch the issue so that no one can exploit it.
6. Insecure source code
The app’s source code is what makes it functional. It’s the fundamentals. If you do not protect your source code, you are effectively giving away your competitive advantage, or intellectual protocol, for nothing. In addition, source code frequently coexists with API or encryption keys, authentication credentials, user passwords, and other sensitive information that must not be exploited.
We do not only mean your source code when we refer to source code. We refer to all of the source code you employ, including code from third parties such as partners or suppliers, as well as straightforward open-source code. If any of these components are insecure, your mobile app security is at risk.
How to prevent insecure source code
You can prevent insecure source code by utilizing mobile app security testing tools that examine your source code frequently or even continuously for vulnerabilities. This can perform most code review work, but you should still conduct manual code evaluations to identify vulnerabilities. Additionally, you should retain your source code securely and grant access to it only to those who require it.
7. Leakage of sensitive data
Data leakage is the exposure of sensitive data online, whether by accident or design. This is what happened to the popular mobile parking app Parkmobile when a third-party software vulnerability led to a data breach that exposed the emails, dates of birth, license plate numbers, and phone numbers of more than 21 million users.
Occasionally, these breaches occur unintentionally. Firebase, for instance, is one of the most popular data storage solutions for Android apps, but it is frequently inadequately configured. Anyone with the correct URL can readily access the databases of an app built with Firebase, exposing sensitive user data.
How to prevent leakage of sensitive data
One method to prevent the leakage of sensitive data is to prevent data caching. Cache-stored data can be used by adversaries to attempt to gain access to a user’s account. Users can explicitly clear the cache, or developers can choose not to cache sensitive data. It may be slightly more inconvenient for the consumers, but it certainly results in a more mobile app security.
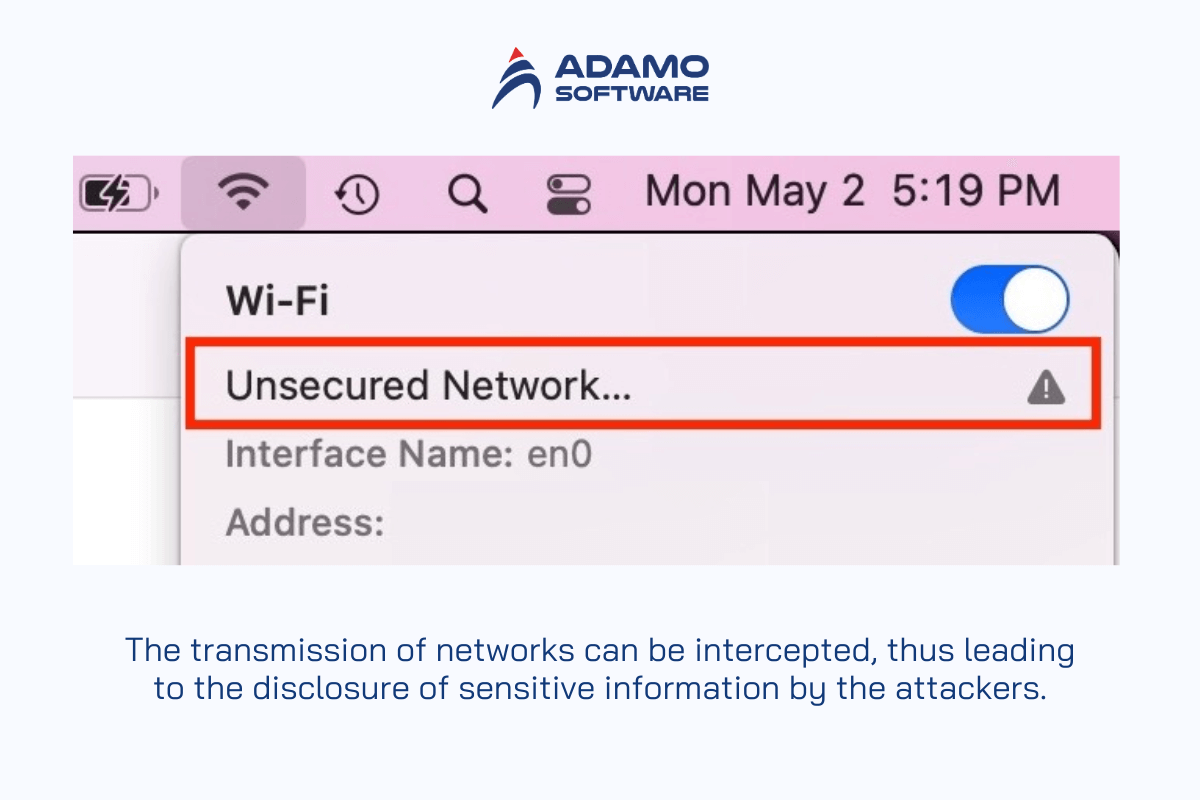
8. Data transmission that is unsafe
Unencrypted or inadequately encrypted data at rest is insecure, so it should come as no surprise that unencrypted data in transit is also insecure. It is not difficult for an adversary to intercept data as it travels over wifi (especially insecure public wifi) or the carrier network of a mobile device.
Although data in transit is frequently encrypted, it is frequently poorly configured, the keys are improperly managed, or the developers use an outdated encryption algorithm. In essence, the same issues as with unencrypted or inadequately encrypted data at rest, with the exception that hackers gain access to it via various channels.
How to prevent unsafe data transmission
Use SSL or TLS protocols to transmit data. Even better, encrypt data before sending it through SSL or TLS, so that there is a second layer of mobile app security in case the SSL or TLS protocol is vulnerable. Moreover, protect data in transit from man-in-the-middle (MitM) assaults with the correct certificate validation and authentication.
9. Insufficient tracking and logging
Once your program is live, you want to track its performance. You need to recognize when mobile app security issues arise so you can respond without negatively impacting the user experience. But you won’t be able to do any of that if you don’t have adequate logging and monitoring systems in place. You will instead be left in the shadows, with information gaps that prevent you from defending against mobile app security incidents.
How to prevent insufficient tracking and logging
The mobile app security solution is to implement or develop a system that logs and monitors all critical application variables. This includes launch time, UI response time, crashes, battery consumption, data consumption, and other mobile app security concerns.
VI. Best Practices Boost Mobile Apps Security
To improve the security of mobile apps, it is crucial to adopt a complex approach based on the use of technologies, strict adherence to industry standards, and the use of preventive measures. Through the practice of IT best practices, developers can protect their applications against different risks and make them safe for users.
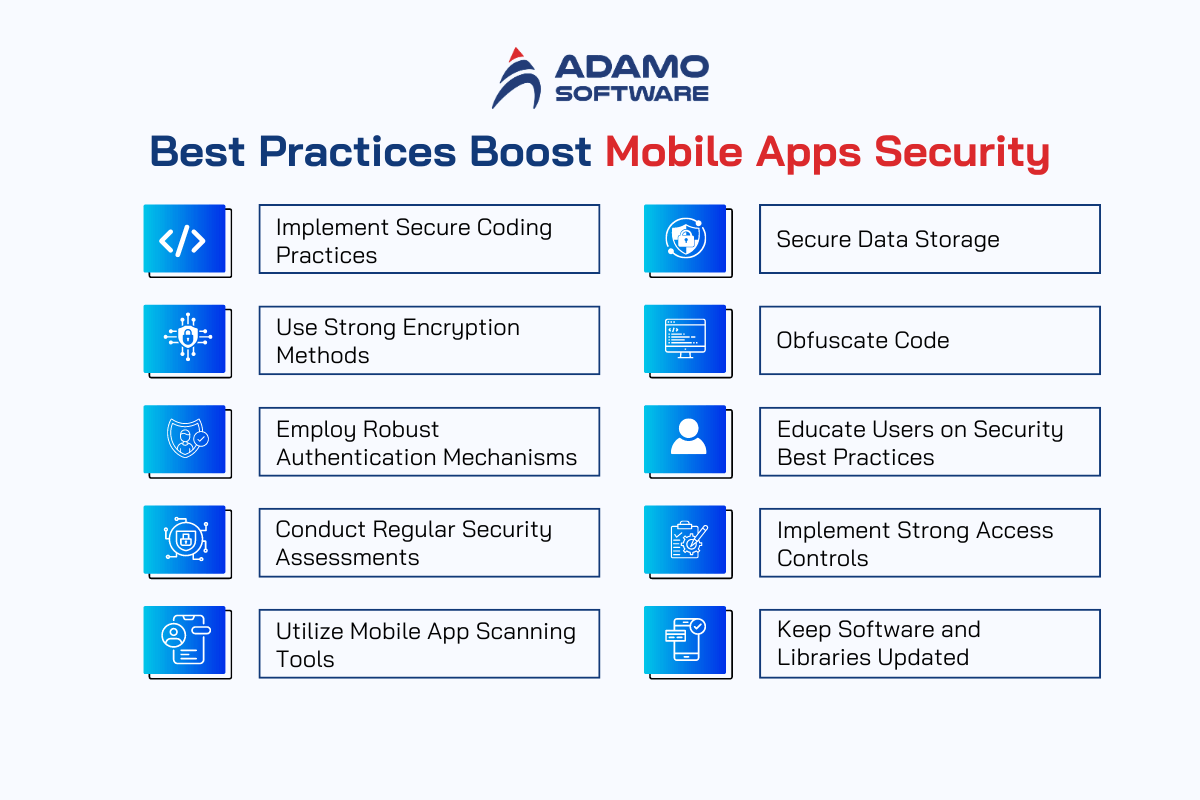
1. Implement Secure Coding Practices
There is a need for developers to follow secure coding best practices to avoid things like buffer overflow, SQL injections, and cross-site scripting. Adhering to the best practices and standards promotes the stability of the application to withstand any existing security vulnerabilities. It is recommended to use a ‘code review’ best practice as well as automated static code analysis tools to detect and eliminate potentially dangerous gaps in the early stages of the development cycle.
2. Use Strong Encryption Methods
It is significant to maintain the confidentiality of the information both during transmission and while it is stored on the device. Encryption and decryption techniques deployed mean that even assuming the data is intercepted, it is still incomprehensible to the intruder. Proper deployment of SSL/TLS for data transfer and encryption of local storage can significantly improve the security of mobile apps.
3. Employ Robust Authentication Mechanisms
Other measures include MFA and BIO, which are more stringent compared to simple passwords. They are effective ways of guaranteeing that only legitimate users access the application and the data. Additional strength to the authentication processes is offered by secure session management practices.
4. Conduct Regular Security Assessments and Penetration Testing
Security audits should be conducted regularly, including vulnerability assessments and penetration testing to evaluate potential risks.
These simulations include assessments to test attacks that portray real-world scenarios to validate the efficacy of existing security controls, thereby providing feedback on potential areas for improvement.
5. Utilize Mobile App Scanning Tools
Automated mobile app scanning tools play a vital role in detecting security vulnerabilities and their remediation. They will do an exhaustive lookup inside the application code, configuration, and network interactions. In-depth reports are provided for the identified issues. In this way, regular scanning would ensure constant monitoring and prompt remediation of vulnerabilities.
6. Secure Data Storage
Implement safe data storage to avoid the chances of data leakage. Sensitive information is stored in an encrypted form. Furthermore, access controls create an entryway only accessible to authorized people. As much as possible, avoid storing sensitive data in local storage and follow safe container practices for such data.
7. Obfuscate Code
Obfuscation of the code makes it very hard to reverse-engineer a mobile app. In turn, this protects the logic and sensitive information of the application. Developers can use code obfuscation techniques, which obscure or even conceal the code from potential misuse by such ill-minded users.
8. Educate Users on Security Best Practices
User education is a vital component of mobile apps security. Informing users about the importance of downloading applications from trusted sources, avoiding unsecured Wi-Fi networks, and recognizing phishing attempts can significantly reduce the risk of security breaches. Providing clear and concise security guidelines within the application can empower users to adopt safer practices.
9. Implement Strong Access Controls
A mobile app has stringent access control measures in place for the sensitive parts, allowing only authorized personnel to access them. RBAC/Least Privilege: It should apply role-based access control and follow the principle of least privilege; this will ensure the risks due to people accessing resources without appropriate business needs are reduced. Regular audits of access controls would be instrumental in keeping them effective.
10. Keep Software and Libraries Updated
Keeping the app, its required software and other tools, up to date is important for keeping a mobile app safe. These updates fix known problems, helping the app stay safe from new dangers.
VII. How Adamo Ensures Mobile Apps Security in Our Software Solution
At Adamo mobile apps security, we consider integration as a primary requirement in our software development process. To mitigate several types of security threats our organization uses a holistic approach that includes both technology-based safeguards along with strict procedures and anticipatory methods. Mobile apps security has not been treated as an afterthought at Safe Zone, rather, it forms a strong foundation of all our software solutions that we offer to clients, from conceptualization to implementation and support.

Secure Development Lifecycle
Adamo abides by a secure SDLC while incorporating security into each phase of our software development process. This essentially means we integrate safe coding practices, frequent peer code reviews, and automatic static code analysis tools to spot and fix any possible vulnerabilities at the earliest opportunity. Following industry standards and guidelines will harden applications against common security threats.
Advanced Encryption Techniques
Adamo adheres to a secure Software Development Life Cycle to build in security in every phase of software development. This would pertain to secure coding practices, periodic reviews of code, and the implementation of state-of-the-art automated static code analysis tools, all aiming at the early detection and fixing of plausible vulnerabilities. Following industry standards and best practices will make our applications resilient to common attacks.
Comprehensive Authentication Mechanisms
We return priority to the protection of sensitive data by advanced encryption techniques; all data is encrypted, both in transit and at rest. To this end, it remains inaccessible to any entity not authorized. That means our security strategy for mobile apps incorporates SSL/TLS protocols for data transmission and secure data storage practices.
Regular Security Assessments and Penetration Testing
Adamo deploys thorough authentication mechanisms to prevent unauthorized access to our applications. In this respect, we use multi-factor and biometric authentication and secure session management to ensure that only properly authorized users can access our applications and their data. These robust authentication methods are designed to provide an additional layer of security and enhance user trust.
Utilization of Mobile App Scanning Tools
Using sophisticated mobile application scanning technologies, we effectively mitigate risks associated with apps. These tools offer a full analysis of our application’s code, settings, and network traffic while reporting findings about discovered deviations. The latter could mean that constant scanning provides for consistent check and repair of the weakness.
Code Obfuscation and Secure Data Storage
This is done to prevent reverse engineering of the applications and data leakage and in turn, Adamo uses code obfuscation and secure storage of data. By wrapping our code, we essentially make it harder for the attackers to penetrate through our applications. Furthermore, we guarantee that any data is securely stored and encrypted, thus minimizing the chances of its confiscation by different individuals.
User Education and Awareness
Adamo believes that user education is critically important in ensuring the security of mobile apps. Our security measures include the use of comprehensive and easily understandable messages to invitee users and the public on how to protect their applications, including creating awareness of the need to download applications from trusted sources and avoiding unsecured W-Fi networks. In other words, the protection of our applications is improved by giving users strength in the form of knowledge.
Continuous Updates and Patching
We understand that it is compulsory to update the software and libraries we have been using frequently. Adamo updates and patches the applications often to fix any uncovered vulnerabilities and to strengthen the security. It also aims to make our software constantly secure from any such threat that might arise in the future.
VII. F.A.Qs about Mobile Apps Security
1. What is mobile apps security?
Mobile app security is a broad term that encompasses all the measures and practices used in the security of mobile applications against security threats and risks. This includes measures like encryption, authentication, secure data management, and constant vigilance to protect the app and the data it contains or processes. Mobile app security is essential to prevent malicious third parties from gaining access to users’ details and eroding customers’ confidence.
2. Why is mobile apps security important?
Mobile apps security is essential since it enhances the security of user data in cases of unauthorized access, cyber-attacks, and data breaches. Focusing on security mobile apps allows companies to follow the regulations and avoid significant financial losses, reputational damage, and user trust loss. As proven in this paper, the integration of mobile application security solutions is crucial in enhancing the well-being and stability of an application and in establishing a safe and reliable platform for users.
3. How do mobile app scanning tools work?
Mobile app scanning tools are comprehensive automatic solutions that check the source code of the application, its settings, and network traffic for potential threats. These tools can do full scans which give out reports of areas that require attention to be given. Routine scanning using mobile app scanning tools ensures that there is a constant check on mobile app security and quick fixes for the security threats that may be discovered.
4. What are some common threats to mobile apps security?
Some of the risks affecting mobile apps security are malware, phishing, insecure connections, limited authentication, leakage of data, weak code obscuration, and MitM. It is important to be familiar with these threats to be able to apply adequate measures for mobile application security. If these vulnerabilities are fixed, developers can design better security mobile applications that protect user information and enhance user security.
5. How can developers enhance mobile app security?
Mobile apps security can be improved by developers practicing secure code writing, using strong encryptions, and implementing strict authentication such as multifactor authentication. It is imperative to perform monthly security audits and assessments such as penetration testing and vulnerability scan. Using the mobile app scanner to periodically scan for threats, proper accreditation of data storage, and giving out security tips are also important strategies. These combined efforts ensure that security mobile apps are well protected against new threats and risks as the future holds.